crashコマンドによるvmcore解析手順
目次
- 概要
- インストール
- 実行
- その他便利コマンド
1.概要
カーネルクラッシュが発生すると、クラッシュダンプ(vmcore)が/var/crash/ディレクトリ下に生成されます。しかし、vmcoreはバイナリファイルであり、そのままでは中身を読むことができません。本記事では、crashコマンドを使用することで、vmcoreの内容を解析する方法について述べます。
2.インストール
crashコマンドを使用するためには、crashコマンドの他にvmlinuxが必要になります。vmlinuxはサイズが2GB以上あります。また、crashコマンドの実行は大きくメモリを消費します。サーバスペックが心許ない場合は、別途障害解析用の環境を用意して解析することをおすすめします。
1.vmcoreから必要なvmlinuxのバージョンを確認します。vmcoreファイルに対して、以下のコマンドを実行します。
strings vmcore | head以下のような出力が得られます。
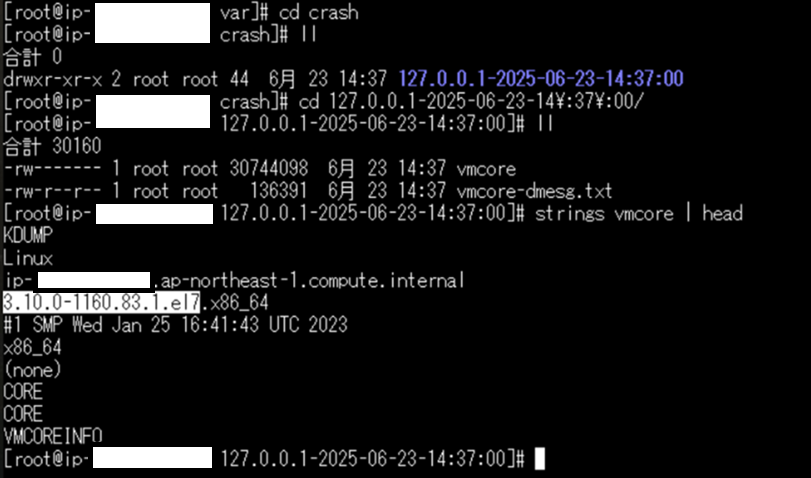
「3.10.0-1160.83.1.el7」の部分が必要になるバージョンです。
2.上記を踏まえて、下記コマンドでvmlinuxをインストールします。「3.10.0-1160.83.1.el7」の箇所は、確認できたバージョンに応じて書き換えてください。
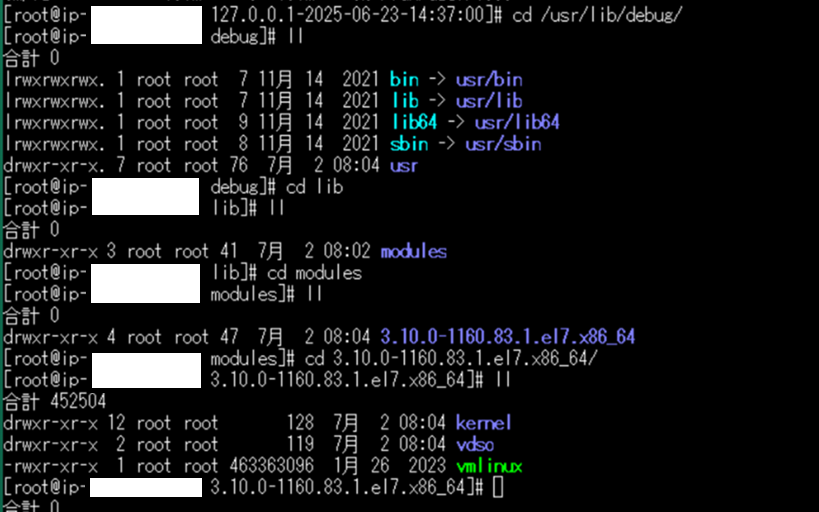
yum install --enablerepo=base-debuginfo kernel-debuginfo-3.10.0-1160.83.1.el7インストールに成功すると、/usr/lib/debug/usr/lib/modules/3.10.0-1160.83.1.el7.x86_64/ディレクトリ下にvmlinuxが格納されているはずです。
3.crashコマンドをインストールします。下記コマンドでインストールできます。
yum install crash3.実行
crashコマンドとvmlinuxの準備ができたら下記コマンドを実行します。構成に応じてファイルのパスは変えてください。
crash /usr/lib/debug/usr/lib/modules/3.10.0-1160.83.1.el7.x86_64/vmlinux /var/crash/127.0.0.1-2025-06-23-14\:37\:00/vmcore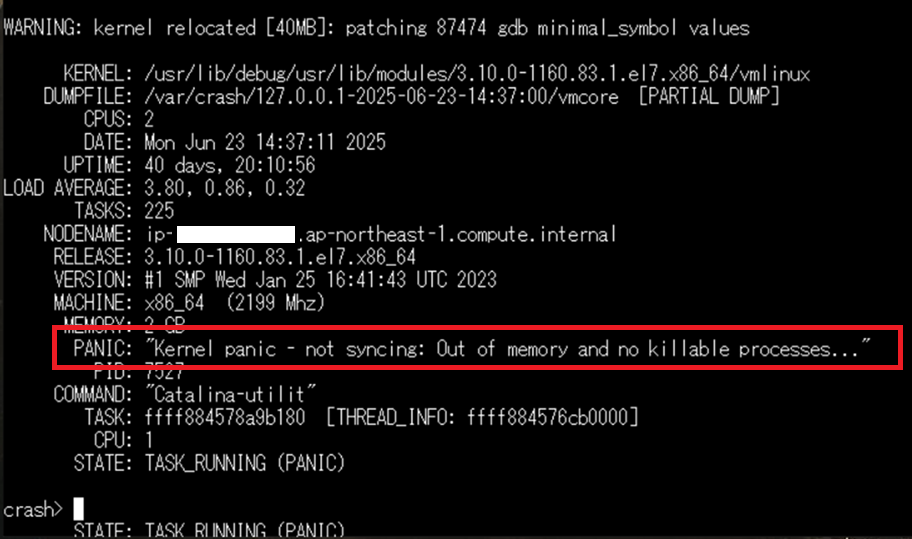
読み込みに成功すると、上記のような出力が得られます。「PANIC」に出力されている内容がカーネルパニックの発生原因です。画像の場合は、「Out of memory and no killable prosesses…」と出ているので、メモリ不足でクラッシュしたことがわかります。
4.詳しく解析する
上記の出力から単純な発生要因についてはわかりますが、具体的にどこの処理で落ちたのかといった原因調査のためにはさらに詳しく見ていく必要があります。crashで使用できるコマンドの一覧については
crash> helpで確認できます。
全てのコマンドを網羅すると膨大になるため、本記事では代表的なコマンドについて紹介します。
crash> mod -Sはモジュールを一括ロードするコマンドです。解析を始める前にとりあえず実行しておくと良いと思います。
crash> mod -s [モジュール名]で個別にロードすることもできます。
また、
crash> modでモジュールの一覧を確認できます。
crash> logは読んで字のごとくログを確認するコマンドです。カーネルパニック発生時の全体像を把握するために、最初に実行することが多いと思います。
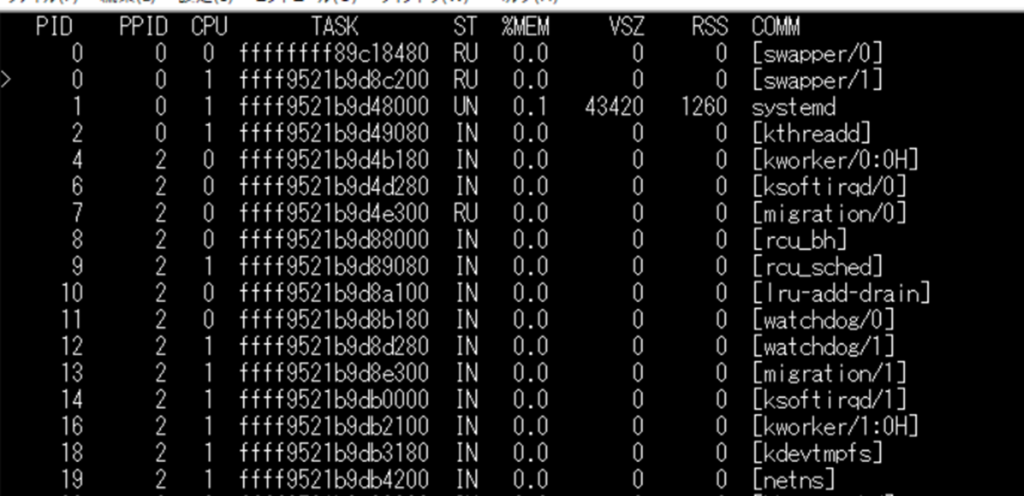
crash> psはカーネルパニック発生時のプロセスを確認することができます。
画像はpsコマンドの出力例です。今回のようなメモリ不足の際には、どのプロセスがメモリを食いつぶしたかの特定に役立ちます。
crash> qでcrashコマンドを終了できます。